2026 IEEE Projects on CRYPTOGRAPHY
Cryptography is the practice and study of techniques for secure communication in the presence of malicious third parties (adversaries). It uses mathematical concepts and a set of rule-based calculations called algorithms to transform readable information (plaintext) into an unintelligible format (ciphertext). The growth of cryptographic technology has raised a number of legal issues in the information age. Cryptography's potential for use as a tool for espionage and sedition has led many governments to classify it as a weapon and to limit or even prohibit its use and export.CRYPTOGRAPHY projects in JAVAIn some jurisdictions where the use of cryptography is legal, laws permit investigators to compel the disclosure of encryption keys for documents relevant to an investigation.Cryptography also plays a major role in digital rights management and copyright infringement of digital media.
Contact: 9591912372
Cryptography or cryptology (from Ancient Greek: κρυπτός, translit. kryptós "hidden, secret"; and γράφειν graphein, "to write", or -λογία -logia, "study", respectively is the practice and study of techniques for secure communication in the presence of third parties called adversaries.More generally, cryptography is about constructing and analyzing protocols that prevent third parties or the public from reading private messages;various aspects in information security such as data confidentiality, data integrity, authentication, and non-repudiation are central to modern cryptography. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, electrical engineering, communication science, and physics. Applications of cryptography include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications.
Cryptography prior to the modern age was effectively synonymous with encryption, the conversion of information from a readable state to apparent nonsense.CRYPTOGRAPHY projects in JAVA The originator of an encrypted message shares the decoding technique only with intended recipients to preclude access from adversaries. The cryptography literature often uses the names Alice ("A") for the sender, Bob ("B") for the intended recipient, and Eve ("eavesdropper") for the adversary.Since the development of rotor cipher machines in World War I and the advent of computers in World War II, the methods used to carry out cryptology have become increasingly complex and its application more widespread. Modern cryptography is heavily based on mathematical theory and computer science practice; cryptographic algorithms are designed around computational hardness assumptions, making such algorithms hard to break in practice by any adversary. It is theoretically possible to break such a system, but it is infeasible to do so by any known practical means. These schemes are therefore termed computationally secure; theoretical advances, e.g., improvements in integer factorization algorithms, and faster computing technology require these solutions to be continually adapted. There exist information-theoretically secure schemes that probably cannot be broken even with unlimited computing power—an example is the one-time pad—but these schemes are more difficult to implement than the best theoretically breakable but computationally secure mechanisms. Symmetric-key cryptography refers to encryption methods in which both the sender and receiver share the same key (or, less commonly, in which their keys are different, but related in an easily computable way). This was the only kind of encryption publicly known until June 1976. logic diagram showing International Data Encryption Algorithm cypher process IEEE Projects on CRYPTOGRAPHY One round (out of 8.5) of the IDEA cipher, used in most versions of PGP and OpenPGP compatible software for time-efficient encryption of messages Symmetric key ciphers are implemented as either block ciphers or stream ciphers. A block cipher enciphers input in blocks of plaintext as opposed to individual characters, the input form used by a stream cipher. The Data Encryption Standard (DES) and the Advanced Encryption Standard (AES) are block cipher designs that have been designated cryptography standards by the US government (though DES's designation was finally withdrawn after the AES was adopted).IEEE Projects on CRYPTOGRAPHY Despite its deprecation as an official standard, DES (especially its still-approved and much more secure triple-DES variant) remains quite popular; it is used across a wide range of applications, from ATM encryption to e-mail privacyand secure remote access.Many other block ciphers have been designed and released, with considerable variation in quality. Many, even some designed by capable practitioners, have been thoroughly broken, such as FEAL. Stream ciphers, in contrast to the 'block' type, create an arbitrarily long stream of key material, which is combined with the plaintext bit-by-bit or character-by-character, somewhat like the one-time pad. In a stream cipher, the output stream is created based on a hidden internal state that changes as the cipher operates. CRYPTOGRAPHY projects in PYTHONThat internal state is initially set up using the secret key material. RC4 is a widely used stream cipher; see Category:Stream ciphers.Block ciphers can be used as stream ciphers; see Block cipher modes of operation. Cryptographic hash functions are a third type of cryptographic algorithm. They take a message of any length as input, and output a short, fixed length hash, which can be used in (for example) a digital signature. For good hash functions, an attacker cannot find two messages that produce the same hash. MD4 is a long-used hash function that is now broken; MD5, a strengthened variant of MD4, is also widely used but broken in practice. The US National Security Agency developed the Secure Hash Algorithm series of MD5-like hash functions: SHA-0 was a flawed algorithm that the agency withdrew;
CRYPTOGRAPHY Projects in PYTHON
Cryptography or cryptology (from Ancient Greek: κρυπτός, translit. kryptós "hidden, secret"; and γράφειν graphein, "to write", or -λογία -logia, "study", respectively is the practice and study of techniques for secure communication in the presence of third parties called adversaries.More generally, cryptography is about constructing and analyzing protocols that prevent third parties or the public from reading private messages;various aspects in information security such as data confidentiality, data integrity, authentication, and non-repudiation are central to modern cryptography. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, electrical engineering, communication science, and physics. Applications of cryptography include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications.
CRYPTOGRAPHY Projects in PYTHON
key information about cryptography:
- Definition: Cryptography, derived from Greek words for "hidden writing," is the science of securing communications and data.
- Core Principles: Modern cryptography aims to provide confidentiality, integrity, authentication, and non-repudiation.
- Confidentiality: Ensures that information is accessible only to the intended recipient, preventing eavesdropping.
- Integrity: Guarantees that data has not been altered or tampered with during storage or transmission.
- Authentication: Confirms the identities of the sender and receiver, verifying the origin of the information.
- Non-repudiation: Prevents a sender from later denying their actions or the authenticity of their signature.
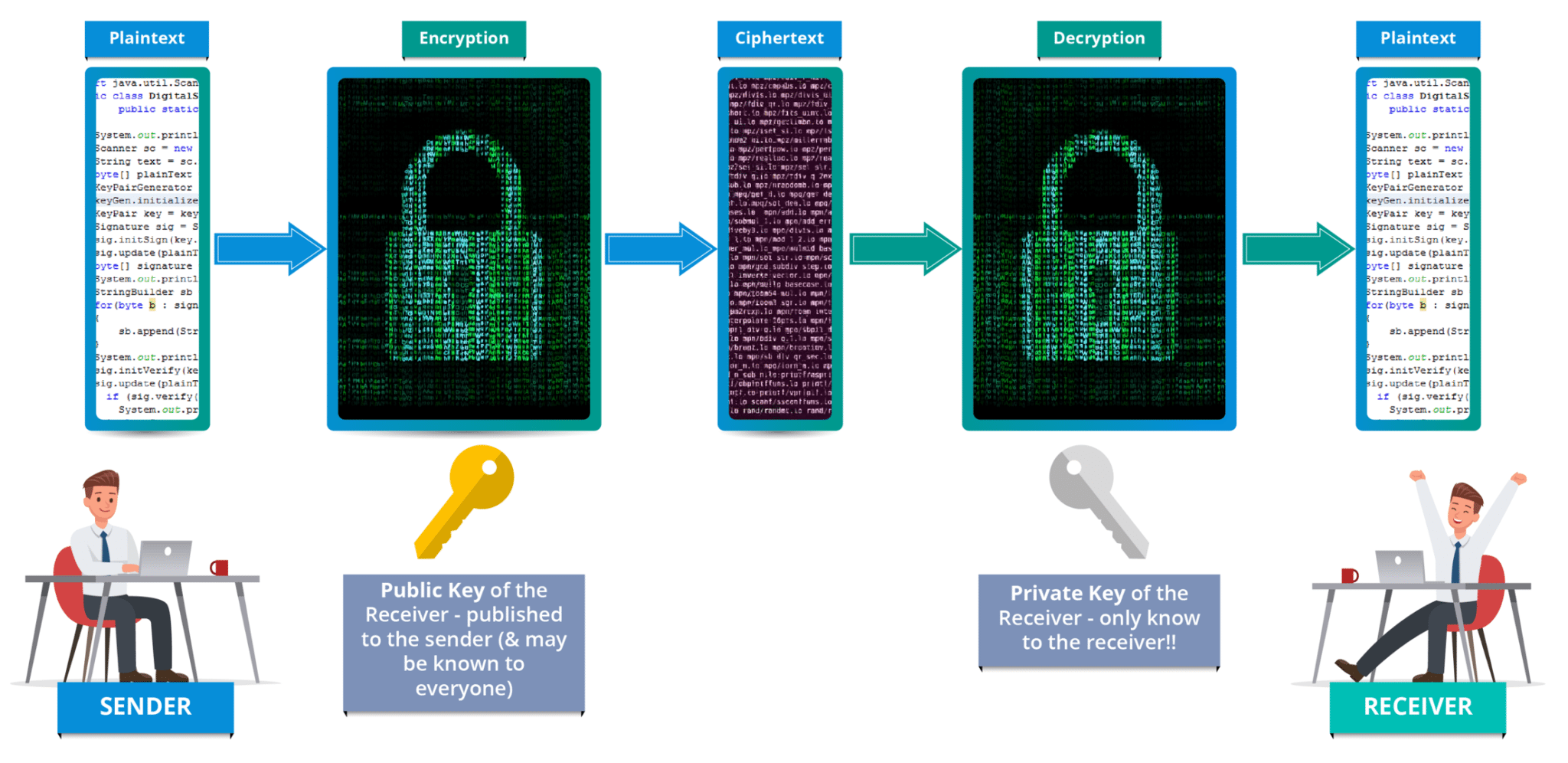
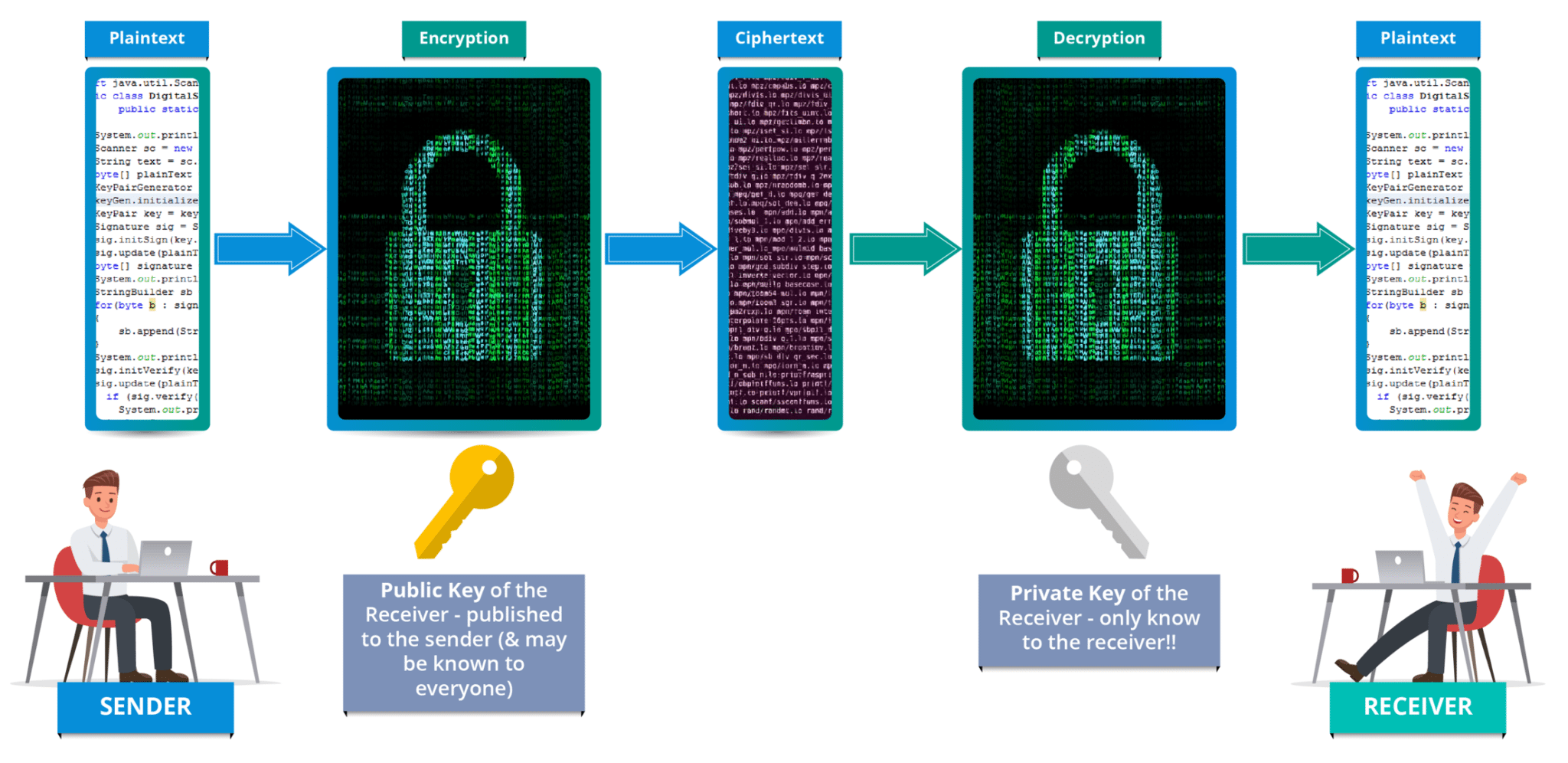
- Plaintext and Ciphertext: Readable data (plaintext) is converted into an unreadable format (ciphertext) through encryption.
- Encryption and Decryption: Encryption is the process of scrambling data, while decryption is the process of converting it back to plaintext using a key.
- Cryptographic Keys: These are strings of characters or bits used with algorithms to control the encryption and decryption process.
- Symmetric Cryptography: Uses a single, shared secret key for both encryption and decryption.
- Symmetric Algorithms: Examples include the Advanced Encryption Standard (AES) and the older Data Encryption Standard (DES), known for their speed and efficiency for bulk data encryption.
- Asymmetric Cryptography: Also known as public-key cryptography, it uses a pair of mathematically related keys: a public key for encryption and a private key for decryption.
- Asymmetric Algorithms: Examples include RSA and Elliptic Curve Cryptography (ECC), used for secure key exchange and digital signatures.
- Hybrid Systems: Most modern systems combine both symmetric and asymmetric cryptography to leverage the speed of the former and the secure key exchange of the latter.
- Hash Functions: These algorithms convert data of any size into a fixed-length "fingerprint" (hash value) and are one-way (irreversible), primarily used for integrity checks and password storage.
- Digital Signatures: Use asymmetric cryptography and hash functions to provide data authenticity, integrity, and non-repudiation, often legally binding.
- Applications: Cryptography is fundamental to secure web browsing (HTTPS/TLS), online banking, email (PGP/S/MIME), cryptocurrencies, and password protection.
- Key Management: The secure generation, storage, and distribution of keys are critical; a compromised key renders the entire system vulnerable.
- Evolution: Cryptography has evolved from simple historical ciphers (like the Caesar cipher) to complex mathematical algorithms based on computational hardness assumptions.
- Future Challenges: The advent of quantum computing poses a potential threat to current public-key algorithms, driving research into new quantum-resistant cryptographic methods.
CRYPTOGRAPHY Projects in JAVA
Cryptography prior to the modern age was effectively synonymous with encryption, the conversion of information from a readable state to apparent nonsense.CRYPTOGRAPHY projects in JAVA The originator of an encrypted message shares the decoding technique only with intended recipients to preclude access from adversaries. The cryptography literature often uses the names Alice ("A") for the sender, Bob ("B") for the intended recipient, and Eve ("eavesdropper") for the adversary.Since the development of rotor cipher machines in World War I and the advent of computers in World War II, the methods used to carry out cryptology have become increasingly complex and its application more widespread. Modern cryptography is heavily based on mathematical theory and computer science practice; cryptographic algorithms are designed around computational hardness assumptions, making such algorithms hard to break in practice by any adversary. It is theoretically possible to break such a system, but it is infeasible to do so by any known practical means. These schemes are therefore termed computationally secure; theoretical advances, e.g., improvements in integer factorization algorithms, and faster computing technology require these solutions to be continually adapted. There exist information-theoretically secure schemes that probably cannot be broken even with unlimited computing power—an example is the one-time pad—but these schemes are more difficult to implement than the best theoretically breakable but computationally secure mechanisms. Symmetric-key cryptography refers to encryption methods in which both the sender and receiver share the same key (or, less commonly, in which their keys are different, but related in an easily computable way). This was the only kind of encryption publicly known until June 1976. logic diagram showing International Data Encryption Algorithm cypher process IEEE Projects on CRYPTOGRAPHY One round (out of 8.5) of the IDEA cipher, used in most versions of PGP and OpenPGP compatible software for time-efficient encryption of messages Symmetric key ciphers are implemented as either block ciphers or stream ciphers. A block cipher enciphers input in blocks of plaintext as opposed to individual characters, the input form used by a stream cipher. The Data Encryption Standard (DES) and the Advanced Encryption Standard (AES) are block cipher designs that have been designated cryptography standards by the US government (though DES's designation was finally withdrawn after the AES was adopted).IEEE Projects on CRYPTOGRAPHY Despite its deprecation as an official standard, DES (especially its still-approved and much more secure triple-DES variant) remains quite popular; it is used across a wide range of applications, from ATM encryption to e-mail privacyand secure remote access.Many other block ciphers have been designed and released, with considerable variation in quality. Many, even some designed by capable practitioners, have been thoroughly broken, such as FEAL. Stream ciphers, in contrast to the 'block' type, create an arbitrarily long stream of key material, which is combined with the plaintext bit-by-bit or character-by-character, somewhat like the one-time pad. In a stream cipher, the output stream is created based on a hidden internal state that changes as the cipher operates. CRYPTOGRAPHY projects in PYTHONThat internal state is initially set up using the secret key material. RC4 is a widely used stream cipher; see Category:Stream ciphers.Block ciphers can be used as stream ciphers; see Block cipher modes of operation. Cryptographic hash functions are a third type of cryptographic algorithm. They take a message of any length as input, and output a short, fixed length hash, which can be used in (for example) a digital signature. For good hash functions, an attacker cannot find two messages that produce the same hash. MD4 is a long-used hash function that is now broken; MD5, a strengthened variant of MD4, is also widely used but broken in practice. The US National Security Agency developed the Secure Hash Algorithm series of MD5-like hash functions: SHA-0 was a flawed algorithm that the agency withdrew;
Projects at Bangalore offers Final Year students Engineering projects - ME projects,M.Tech projects,BE Projects,B.Tech Projects, Diploma Projects,Electronics Projects,ECE Projects,EEE Projects,Mechanical projects,Bio-Medical Projects,Telecommunication Projects,Instrumentation Projects,Software Projects - MCA Projects,M.Sc Projects,BCA Projects,B.Sc Projects,Science Exhibition Kits,Seminars,Presentations,Reports and so on...